I plan to make a concerted effort to refine my writing skills and not let my technical skillset atrophy since I have been focused on more project management during my day job lately.
One area in which I don't have much practical experience is internal pentests. I've done maybe five of them in the past few years, and it seems like a ton of fun. Since it feels like hacking, you going after a relatively soft internal network versus banging away at a web application or against an organization's external perimeter.
Enter https://ludus.cloud - an easy-to-use cyber range software that feels like it should cost a lot of money because of how polished it is. If you have experience with Ansible, the platform should be easy to pick up.
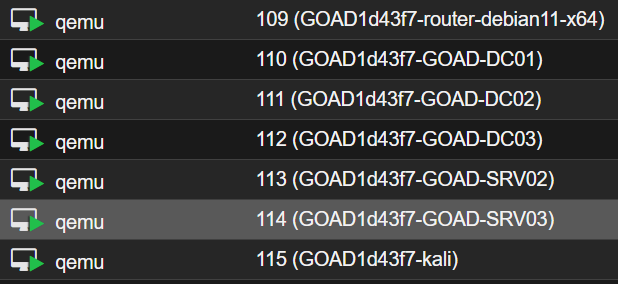
Since I wanted to work on my internal Windows hacking skillset, I looked at the de-facto standard for this type of thing, and that is GOAD (Game of Active Directory) https://github.com/Orange-Cyberdefense/GOAD. You can deploy this vulnerable AD environment with ludus to work through specific vulnerabilities and attack paths that simulate a vulnerable internal network.
The goal for the weekend was to get this deployed with ludus, and I was able to complete it.
Coming up next is an exploration into initial recon and enumeration of the environment.